The Windows 11 23H2 feature update, also known as the Windows 11 2023 update, is now available. If you have applied the latest quality update, the new features of Windows 11 version 23H2 are already Included in Windows 11 22H2. However, the new features have not been activated yet.
These new features will remain Inactive until you use the “enablement package”, a small payload to activate these new settings. The enablement package (eKB) makes it easier to update to 23H2 with just one Restart and reduces the time it takes to complete the upgrade process.
If you prefer, you can manually download an Enablement package, KB5027397. When using Windows 11, version 22H2, you should install it on top of the latest quality updates.
An alternative method is to use the Intune admin center to upgrade your Windows 11 22H2 devices to Windows 11 23H2 by simply creating a Feature update policy.
Utilizing a Feature Updates policy in Intune allows you to choose the specific Windows feature update version for your organization’s devices. This effectively locks that feature update version on all devices.
For instance, if you set up your devices to operate on Windows 11 23H2 using a feature update profile, all devices will stay at this specific feature update level.
Windows Feature update policies and Update Rings policies prevent a device from receiving a feature update version beyond the specified value in the feature update policy.
Related: How to Upgrade Windows 11 Pro to Enterprise
Table of Contents
Prerequisites
- Windows 11 devices must be Enrolled and managed by Intune
- Users of the Devices should be assigned one of the following licenses:
- Windows 10/11 Enterprise E3 or E5 (included in Microsoft 365 F3, E3, or E5)
- Windows 10/11 Education A3 or A5 (included in Microsoft 365 A3 or A5)
- Windows Virtual Desktop Access E3 or E5
- Microsoft 365 Business Premium
- Devices can be either Entra joined, or Entra Hybrid joined.
- Following Windows 10 and Windows 11, Editions are supported:
- Pro/Education/Enterprise/Pro Education/Pro for Workstations.
- Telemetry/Diagnostic data sharing with Microsoft should be Enabled and set to Required level.
- Microsoft Account Sign-in Assistant service (wlidsvc) should not be disabled. It needs to be kept Manually triggered.
When you have an Update Ring policy, set the “Feature update deferral period (days)” to 0 to avoid any delays in delivering feature update to devices via Feature update policy.
Recommended
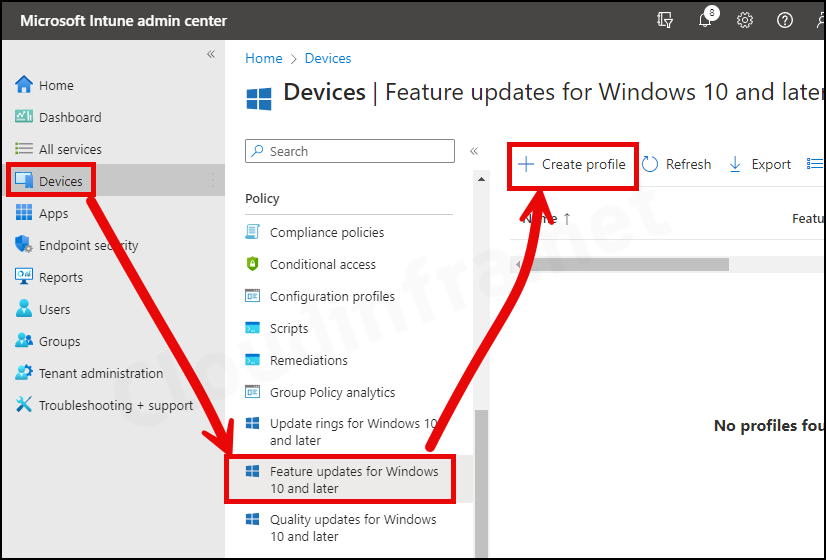
Step 1 – Create a Feature Update Policy
To create a feature update policy, follow the below steps:
- Sign in to the Intune admin center.
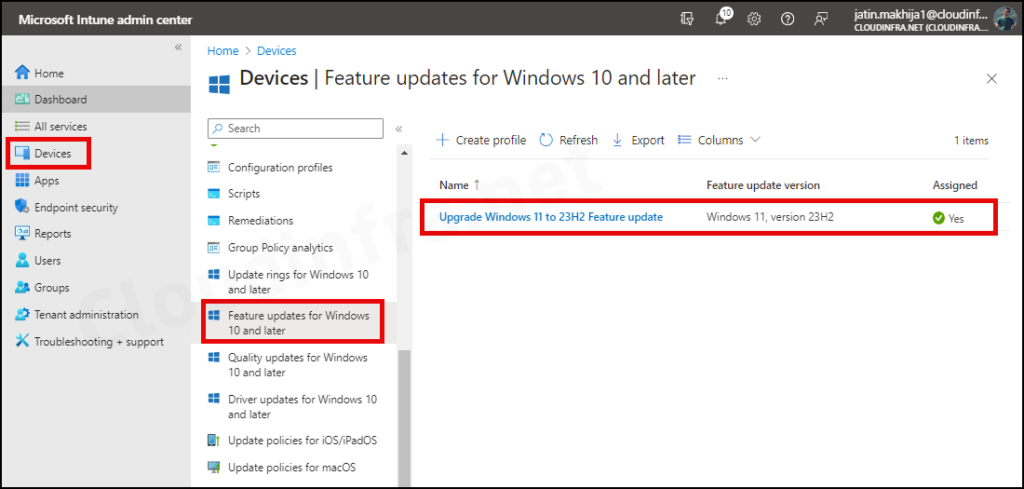
- Click on Devices > Feature update for Windows 10 and later.
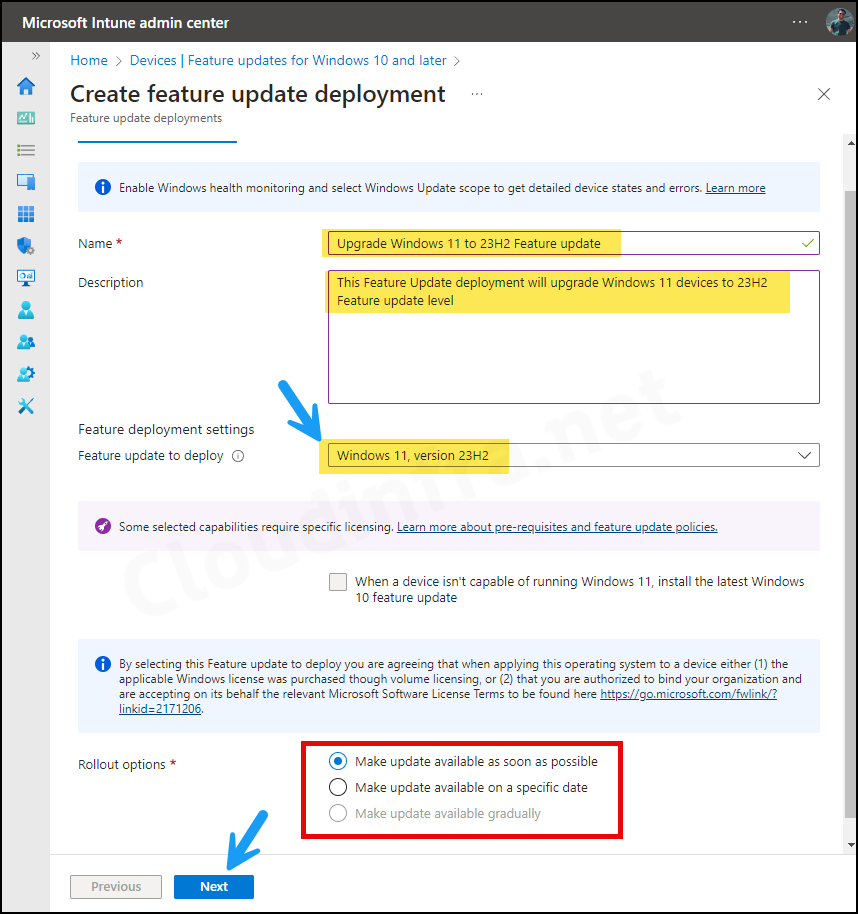
Deployment settings
On the Deployment settings tab, Configure below options:
- Name: Provide the name of the Feature update policy
- Description: Provide a useful description.
- Feature update to deploy: Use the drop-down to select Windows 11, version 23H2.
- Rollout options: There are three roll-out options:
- Make update available as soon as possible – This is the default option selected, It will deploy feature update on users devices without delay.
- Make update available on a specific date – You can select the day you want this feature update to be available for targeted devices.
- Make update available gradually – You can provide a range of time to make the updates available to devices. Intune will automatically create a subset of target devices based on the range configured and the duration mentioned between those days. For more information, refer to the link: Make updates available gradually.
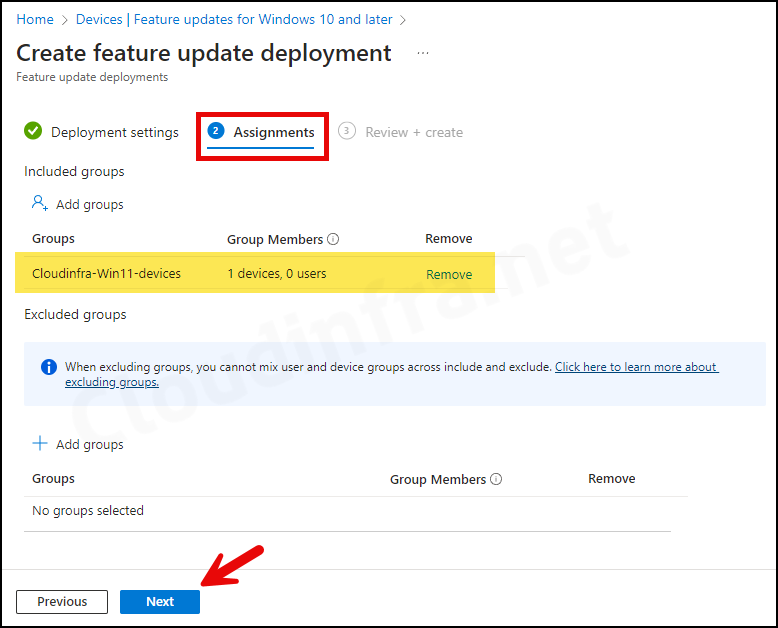
Assignments
Now, you can assign this Feature update deployment to the devices you want to upgrade. Click on Add group and select an Entra security group containing Windows devices. Click Next.
Review + create
Review the Deployment Summary and click on the Create button.
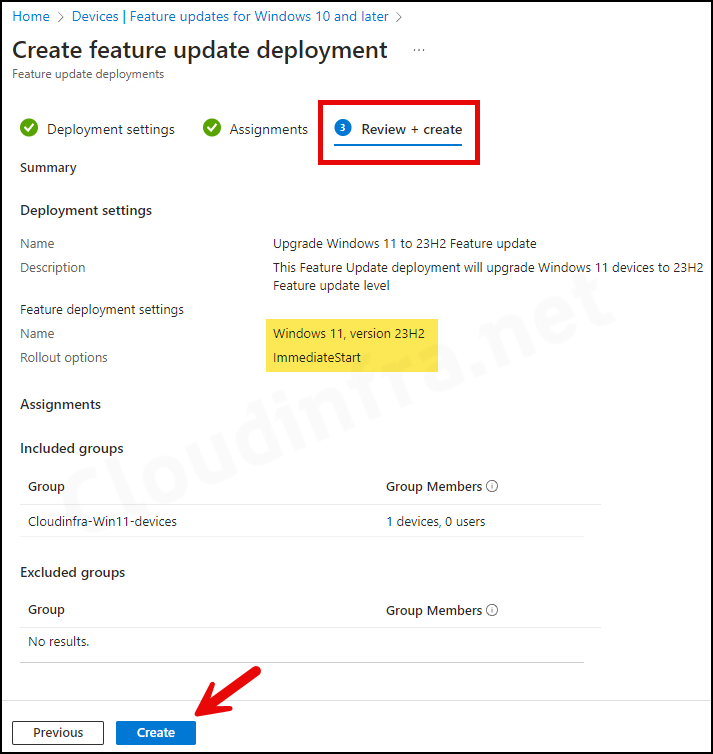
- The feature update profile has been created successfully.
End-user Experience
Once this feature update deployment profile is applied to users’ devices, they will receive a notification and need to reboot to finalize the installation process.
User does not need to take any action to get this feature to update the deployment profile on their devices. Windows devices regularly check in with Intune for new policy updates.
However, if you want to speed up this process, you can force an Intune sync from the device. A restart of the device also triggers the Intune device check-in process.
Troubleshooting
If there are any issues with the Windows 11 23H2 feature update deployment, there are multiple places to investigate and find out what went wrong.
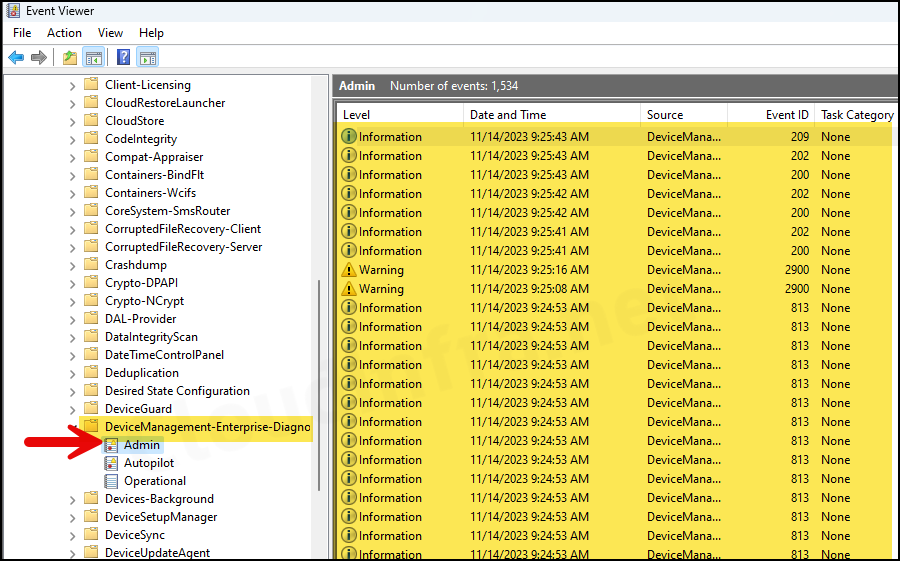
1. Investigate Event Viewer logs
To start with your troubleshooting, you can check the Event Viewer logs on the target device. Follow the below steps to check:
- Press Windows Key + R to open the Run dialog box.
- Type eventvwr and press Enter to open Event Viewer.
- Navigate to Application and Services logs > Microsoft > Windows > DeviceManagement– Enterprise-Diagnostics-Provider > Admin.
2. Check if Safeguard hold is applied
If a device has a Safeguard hold applied for a feature update version deployed through Intune, the upgrade may not proceed. Refer to this link to learn more about opting out of Safeguard Hold.
3. Check Reports on Intune admin center
Export Feature update reports to investigate the deployment’s status. Confirm that the deployment is in the offering state; the update won’t be deployed if it’s paused or scheduled. For instructions on exporting Feature update reports, refer to the link: 3 Ways to Export Windows Feature Update Report from Intune.
4. Check if Telemetry level is set to the Required
Sometimes, if the Telemetry level is not set to Required, Feature updates via Intune may not be offered to the devices. Ensure the Telemetry or Diagnostic data setting is set to Required. For more information on Telemetry/Diagnostic data settings, refer to Intune: Configure Windows Telemetry/Diagnostic data [3 ways].
