In this blog post, I will show you the steps to block emails based on file attachment extension in Microsoft 365. Blocking high-risk attachment types is a practical way to reduce malware delivery via email, especially for file formats that are not business critical. A common example is OneNote (.one), which has been abused in phishing campaigns to deliver malware through embedded content that users are tricked into executing.
In this post, I will show you the best supported ways to block email attachments by file type in Microsoft 365. I will also demonstrate the differences between Exchange Online mail flow rules and the common attachments filter in anti-malware policies so you can choose the right control for your environment. Let’s understand the background of why you may want to block such emails, and then we will explore the steps to create rules in Exchange Online for this.
Contents
Background
Rapid7 observed threat actors distributing malware using OneNote attachments, where users are socially engineered to click embedded content that leads to execution chains such as scripts and payload downloaders. If your organization does not require OneNote files via email, blocking .one at the mail gateway is a reasonable mitigation. Refer to the link for more details: Rapid7 observes use of Microsoft OneNote to spread Redline Infostealer | Rapid7 Blog.
Microsoft OneNote is a digital note-taking application that comes bundled with Microsoft 365. When you install Microsoft 365 on your device, OneNote is typically included. OneNote itself is not a malicious application. However, there have been reports of .one file extensions being exploited to distribute malware, potentially leading to data theft from your computer.
Users may receive phishing emails that contain Microsoft OneNote file attachments. When users open such a file, they are given a button that says Double Click to View File. Certain batch script files are executed in the background when users click this button. According to Rapid 7’s analysis, the malware can steal various data types, including cryptocurrency wallet credentials, Discord data, and web browser data, including cached cookies.
If you want to search for emails that users have received with file attachments using the .one extension or any other attachment type, refer to the blog post Audit report of emails with Specific File Attachment Extension in Microsoft 365.
Block emails with .One file attachment extension
We will explore different options for blocking emails with .one file attachments, both inbound and outbound. The same steps can also be used to block other file attachment extensions.
Option 1: Create a Rule in Exchange Online
This method blocks messages when an attachment’s filename extension matches values you specify. It is easy to implement and useful for quick response.
- Sign in to the Exchange Admin Center using your Global Administrator or Exchange Administrator role.
- Go to Mail Flow and then click on Rules.
- Click on +Add a rule > Create a new rule.
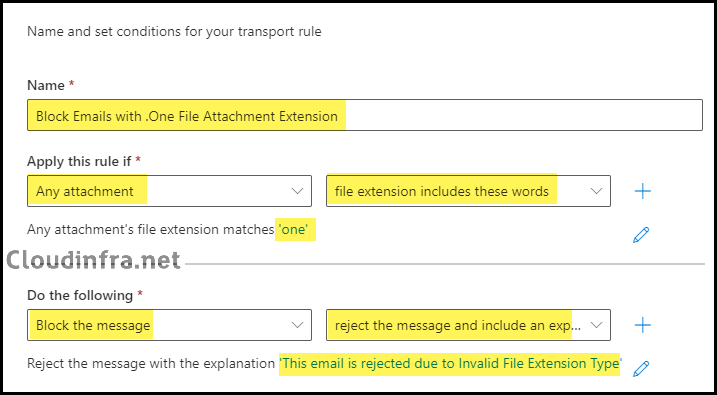
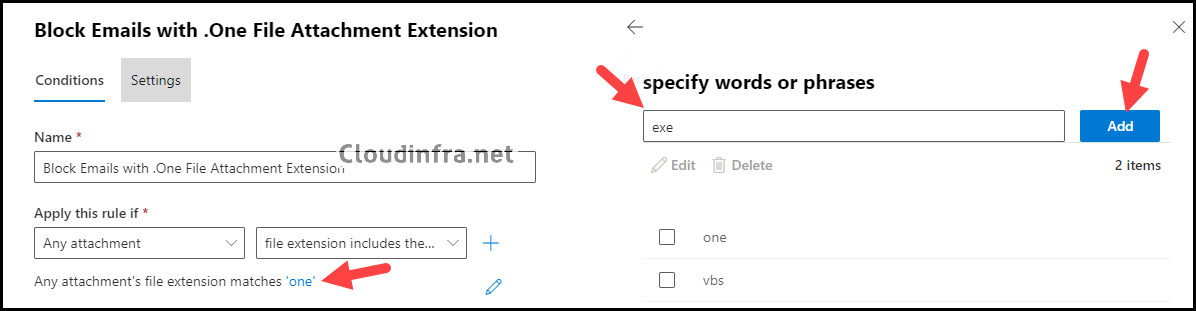
- Rule conditions:
- Name: Block Emails with .One File Attachment Extension
- Apply this rule if: Any attachment and file extension include these words.
- Specify words or phrases: one [without the dot]
- Do the following: Block the message and reject the message and include an explanation.
- Specify rejection reason: This email is rejected due to invalid file extension type.
- Click on Next to proceed.
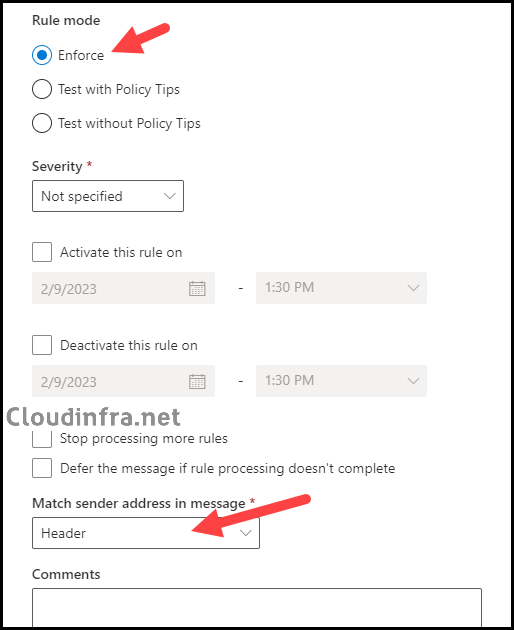
- Rule settings:
- Rule Mode: Enforce
- Keep the rest of the settings at default.
- Click on Next to Proceed.
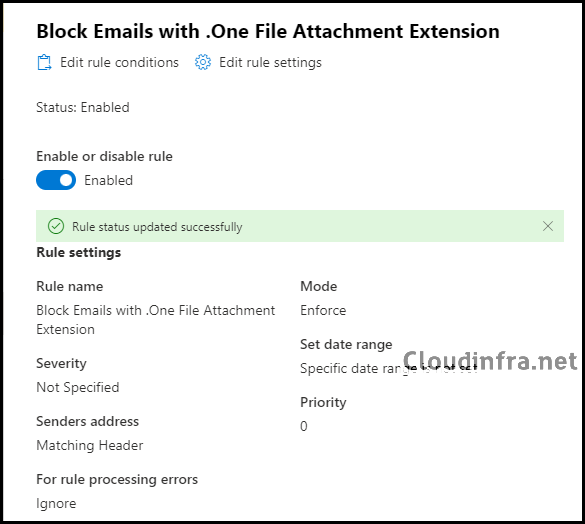
- Review and finish: Review the rule conditions and settings you’ve configured and click Finish to create this rule. Please be aware that the rule is initially created in a disabled state, so you must enable it after it’s been created.
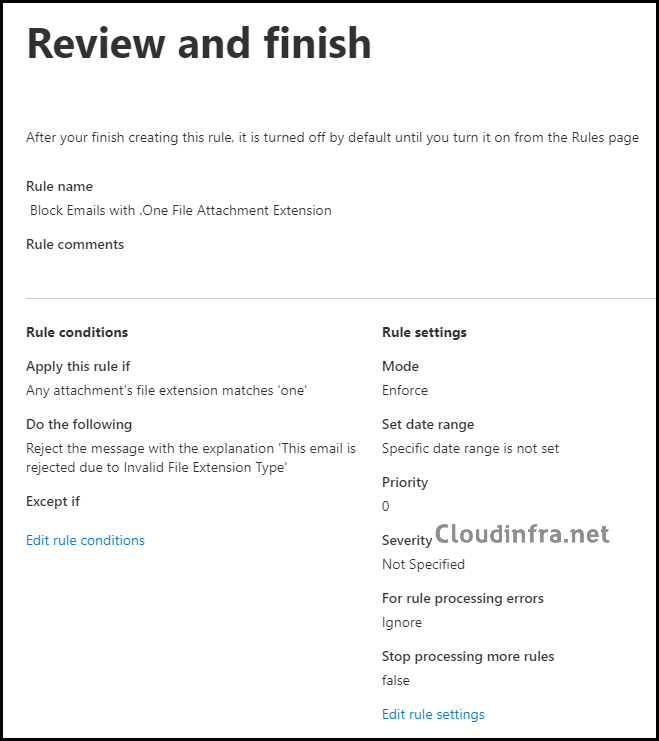
- The rule has been created, but as previously mentioned, it is initially disabled. This means it will not be active or impact any users. To make it effective, the rule needs to be enabled.
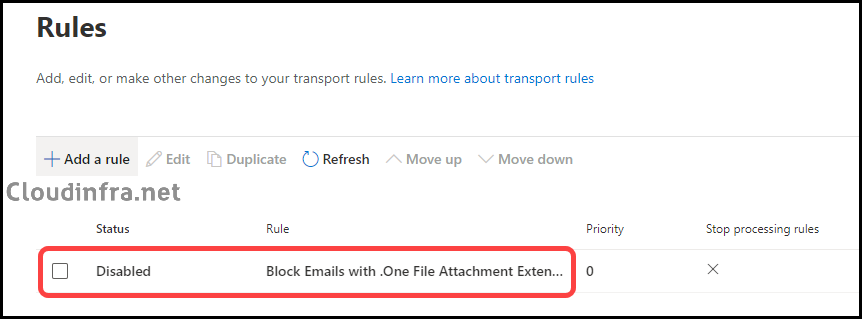
- You can activate the rule by clicking on it and switching the toggle to the “Enable” position.
You can create the same rule using PowerShell as well.
- Install Exchange Online PowerShell module.
- Connect to Exchange Online
Connect-ExchangeOnline
- Run below PowerShell command to create the rule to block attachments with .one file extension, modify the values as required:
New-TransportRule -Name "Block .one attachments (extension)" ` -AttachmentExtensionMatchesWords "one" ` -RejectMessageReasonText "Blocked attachment file type (.one)." ` -StopRuleProcessing $trueCreate an Exchange Online transport rule using PowerShell (extension match)
Option 2: Create an Anti-Malware Policy
In the earlier section, we set up a rule in Exchange Online to block emails containing .one file attachments. Another option for rejecting such emails is to create an anti-malware policy. You can create a new anti-malware policy specifically for blocking .one file extensions or modify the existing default anti-malware policy to include this block. Here, we’ll create a new custom anti-malware policy for blocking .one file extensions.
When configuring the anti-malware policy, you have two actions you can choose from for emails with the .one file extension. You can either reject the message and send a non-delivery receipt (NDR) to the sender or quarantine the message using the attachment filter.
Let’s check the steps:
- Sign in to the Microsoft 365 Defender portal as a Security Administrator or Global Administrator.
- Go to Email and collaboration > Policies & Rules > Threat Policies.
- Under Policies > Find Anti-malware.
- Click on + Create.
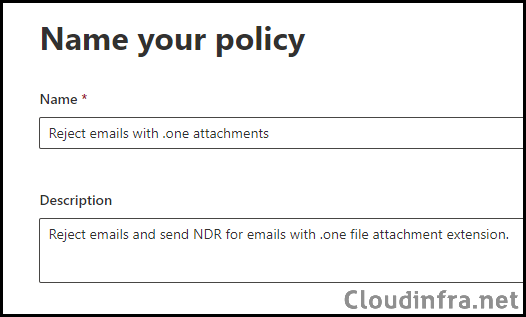
- Name your policy:
- Name: Reject emails with .one attachments
- Description: Reject emails and send NDR for emails with .one file attachment extension.
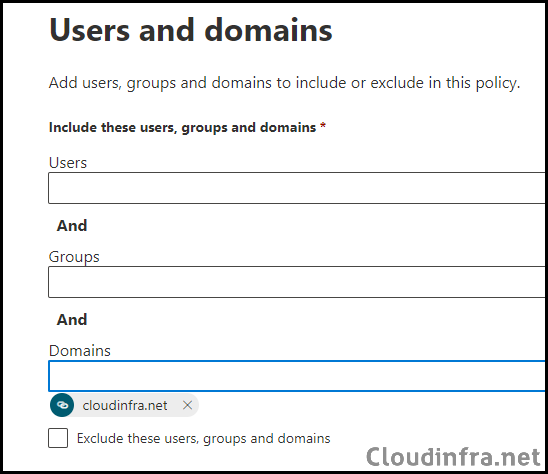
- Users and domains: Add the User, Group, or Domain to which you want to apply this policy. If you add a User, Group, and Domain together, all conditions must match for the rule to take effect.
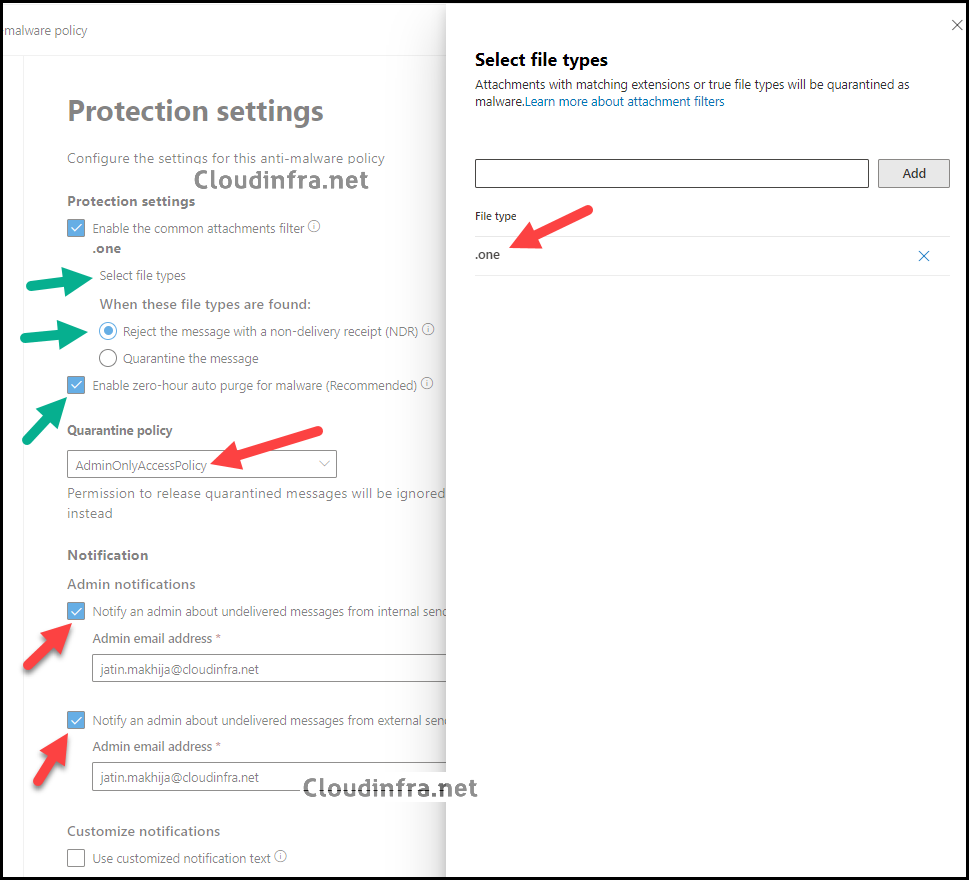
- Protection Settings: Configure protection settings as per below:
- Click on Select file types and add the .one file type to the list of extensions. Click the X icon next to all other file types to remove them.
- When these file types are found: Select Reject the message with a non-delivery receipt (NDR). (An NDR email will be sent to the sender. The message will not be quarantined, and no recipient or admin notifications will be sent).
- Enable ZAP (Zero-hour auto purge): Malware ZAP quarantines messages that are found to contain malware after they have been delivered to Exchange Online mailboxes.
- Quarantine Policy: You can select AdminOnlyAccessPolicy to prevent the user from viewing or releasing the messages.
- Notification: Include admin email addresses for internal and external senders for undelivered emails.
- Click on Submit.
You can create the same rule using PowerShell as well:
- Install Exchange Online PowerShell module.
- Connect to Exchange Online
Connect-ExchangeOnline
- Run below PowerShell command to create the rule to block attachments with .one file extension; modify the values as required:
New-MalwareFilterPolicy -Name "Block OneNote attachments" ` -EnableFileFilter $true ` -FileTypes "one" ` -FileTypeAction RejectNew-MalwareFilterRule -Name "Block OneNote attachments" ` -MalwareFilterPolicy "Block OneNote attachments" ` -SentToScope NotInOrganization ` -Priority 0Create an anti-malware policy that blocks .one using the common attachments filter
Testing of Exchange Online Rule
We’ve created a rule to block all emails with file attachments having the .one extension. To verify this, follow these testing steps:
- Send a test email with a .one file attachment from an external domain to your organization’s internal domain. [Inbound]
- Send a test email with a .one file attachment from your organization’s internal domain to any external domain. [Outbound]
- Send one test email with .one file attachment from an internal domain to an internal domain.
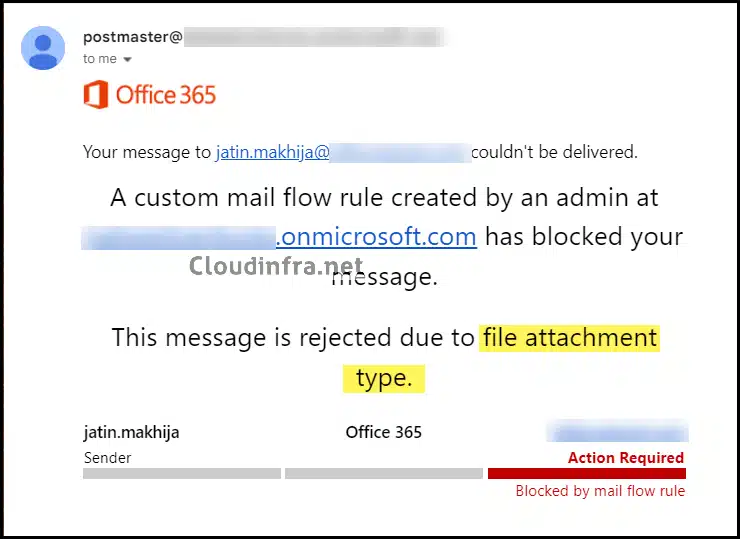
Anyone attempting to send an email with a .one file attachment will receive a bounce-back email with the following message.
“Your message to xxx@cloudinfra.net couldn’t be delivered. A custom mail flow rule created by an admin at xxx.onmicrosoft.com has blocked your message. This message is rejected due to file attachment type.
FAQs
1. How to block other dangerous file extension types using Exchange Online
To further enhance security, you can add more file extensions to the existing rule that blocks .one attachments. Go to the Exchange admin center, navigate to Mail flow > Rules, select the rule created for .one file attachments, and edit its conditions. Under Extensions, add any additional file extensions to the list.
2. I am getting below error message when creating an Exchange rule
Failed to create the new transport rule
Error:
Error executing cmdlet: |Microsoft.Exchange.Data.DataValidationException|Name: The property “Name” with value ” Block Emails with .One File Attachment Extension” is invalid. The value can’t contain leading or trailing whitespace. Exception of type ‘Microsoft.Exchange.Management.PSDirectInvoke.DirectInvokeCmdletExecutionException’ was thrown.
Solution:
- Ensure the rule name does not contain leading or trailing spaces. You can edit the rule name to remove any extra spaces if required.
- Make sure the extension value does not include a dot (.). If you add an extension with a dot, such as .one, you may encounter an error prompting you to remove it. To create the rule successfully, specify the extension without the dot, for example, one.
3. What’s the default anti-malware policy in Microsoft 365? Can it be deleted?
The built-in anti-malware policy in Microsoft 365 is called Default. It holds the lowest priority and is automatically applied to all recipients within your organization. The priority of the default policy remains fixed, and administrators can view, edit, and configure it to align with their organizational requirements. However, it cannot be deleted.
4. How do you manage anti-malware policies using Powershell?
To manage anti-malware policies using PowerShell, follow these steps:
- Install Exchange Online PowerShell module using the Install-Module ExchangeOnlineManagement command.
- Connect to Exchange Online using Connect-ExchangeOnline.
- Use Get-MalwareFilterPolicy or Get-MalwarefilterRule to fetch the existing policy settings.
Creating anti-malware policies using PowerShell is a two-step process. First, you need to create a malware filter policy. Then, you create a malware filter rule that specifies which malware filter policy is applied to the rule.
- New-MalwareFilterPolicy: Use this cmdlet to create a malware filter policy.
- New-MalwareFilterRule: Use this cmdlet to create a malware filter rule.
Modify existing malware filter policy:
- Set-MalwareFilterPolicy: Use this cmdlet to modify malware filter policies.
- Set-MalwareFilterRule: Use this cmdlet to modify malware filter rules.
Conclusion
In this blog post, we’ve learned how to block emails with file attachments using the .one extension. You can also add extensions to the block list to prevent other dangerous extension types .exe or .vbs. You can find the list of dangerous extensions in the default anti-malware policy on the Microsoft Defender portal.
There is a default anti-malware policy that quarantines any message with the below dangerous extensions:
ace, apk, app, appx, ani, arj, bat, cab, cmd,com, deb, dex, dll, docm, elf, exe, hta, img, iso, jar, jnlp, kext, lha, lib, library, lnk, lzh, macho, msc, msi, msix, msp, mst, pif, ppa, ppam, reg, rev, scf, scr, sct, sys, uif, vb, vbe, vbs, vxd, wsc, wsf, wsh, xll, xz, z
Other pre-defined file types can be added to the anti-malware policy:
7z, 7zip, a, accdb, accde, action, ade, adp, appxbundle, asf, asp, aspx, avi, bin, bundle, bz, bz2, bzip2, cab, caction, cer, chm, command, cpl, crt, csh, css, der, dgz, dmg, doc, docx, dot, dotm, dtox, dylib, font, gz, gzip, hlp, htm, html, imp, inf, ins, ipa, isp, its, jnlp, js, jse, ksh, lqy, mad, maf, mag, mam, maq, mar, mas, mat, mav, maw, mda, mdb, mde, mdt, mdw, mdz, mht, mhtml, mscompress, msh, msh1, msh1xml, msh2, msh2xml, mshxml, msixbundle, o, obj, odp, ods, odt, one, onenote, ops, package, pages, pbix, pdb, pdf, php, pkg, plugin, pps, ppsm, ppsx, ppt, pptm, pptx, prf, prg, ps1, ps1xml, ps2, ps2xml, psc1, psc2, pst, pub, py, rar, rpm, rtf, scpt, service, sh, shb, shtm, shx, so, tar, tarz, terminal, tgz, tool, url, vhd, vsd, vsdm, vsdx, vsmacros, vss, vssx, vst, vstm, vstx, vsw, workflow, ws, xhtml, xla, xlam, xls, xlsb, xlsm, xlsx, xlt, xltm, xltx, zi, zip, zipx.

The mail flow rules doesn’t seem to work. Had an email with a .htm attachment come through?
Make sure you do not have a dot in the name while creating a rule. Any attachment file Extension matches “htm”